The old idea of physically engaging with a form of security exploit in order to have it infect your system is no longer completely true, as Trend Micro has this week discovered something rather interesting.
Instead of knowing that you need to click, a new Trojan variation discovered written about by its security experts on the Trend Labs Security Intelligence blog cites that something as simple as hovering your mouse over an infected link could see the payload delivered to your computer and executed.
This is a dramatic difference from the usual way we get infected, which usually requires a bit of human intervention and the touch or click of a file. Granted, people tend to be tricked into firing these files up, downloading a payload under false pretences, but it still requires the click, and doesn’t just run automatically when a mouse cursor hovers over the link.
Yet in the case of the “OTLARD” banking Trojan, that’s exactly what happens, with a recent variant disguised inside of a PowerPoint file, affecting one link in the slideshow.
The rather curious attack arrives in a PowerPoint file that can be opened by the victim, and while the file has to be downloaded to fire up, from there all that needs to be done is for someone to hover over an infected link with a bit of code behind it that downloads the malware and infects your machine.
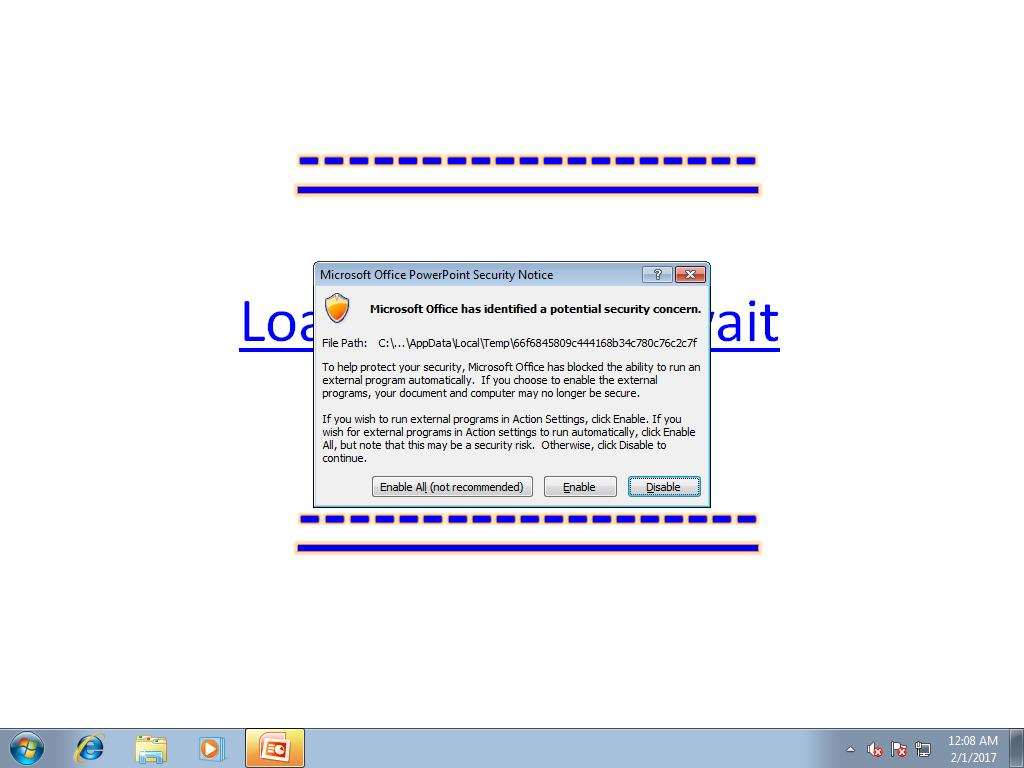
While the technique still technically requires a download of a PowerPoint presentation, the right wording in an email could make this very easy, with all that’s needed being one email from a friend, a co-worker, or client convincing you that the presentation is related to something you may or may not have spoken about, or even possibly worked on.
There is an upside to this, with Trend Micro’s team citing that the trick “will not work in Microsoft PowerPoint Online or Office 365’s “web mode””, meaning if you regularly use PowerPoint in these systems, you’re fine.
In fact, if you rely on recently updated internet security programs, you should also be in the clear, just make sure to keep those security signatures up-to-date, of course.
And as always, be careful what you click, because this is one crafty little file, and chances are that it won’t be alone, with more nasty tricks like it on the way.