There are a lot of scams out there and a lot of scammers attempting to fleece people out of their money, and they won’t stop just because a weekend means you’re supposed to be relaxing. They can come on any day and affect anyone.
This weekend was a good example of that, as a good number of people appear to have been sent the same message purporting to be from the Australian government, but clearly being a scam.
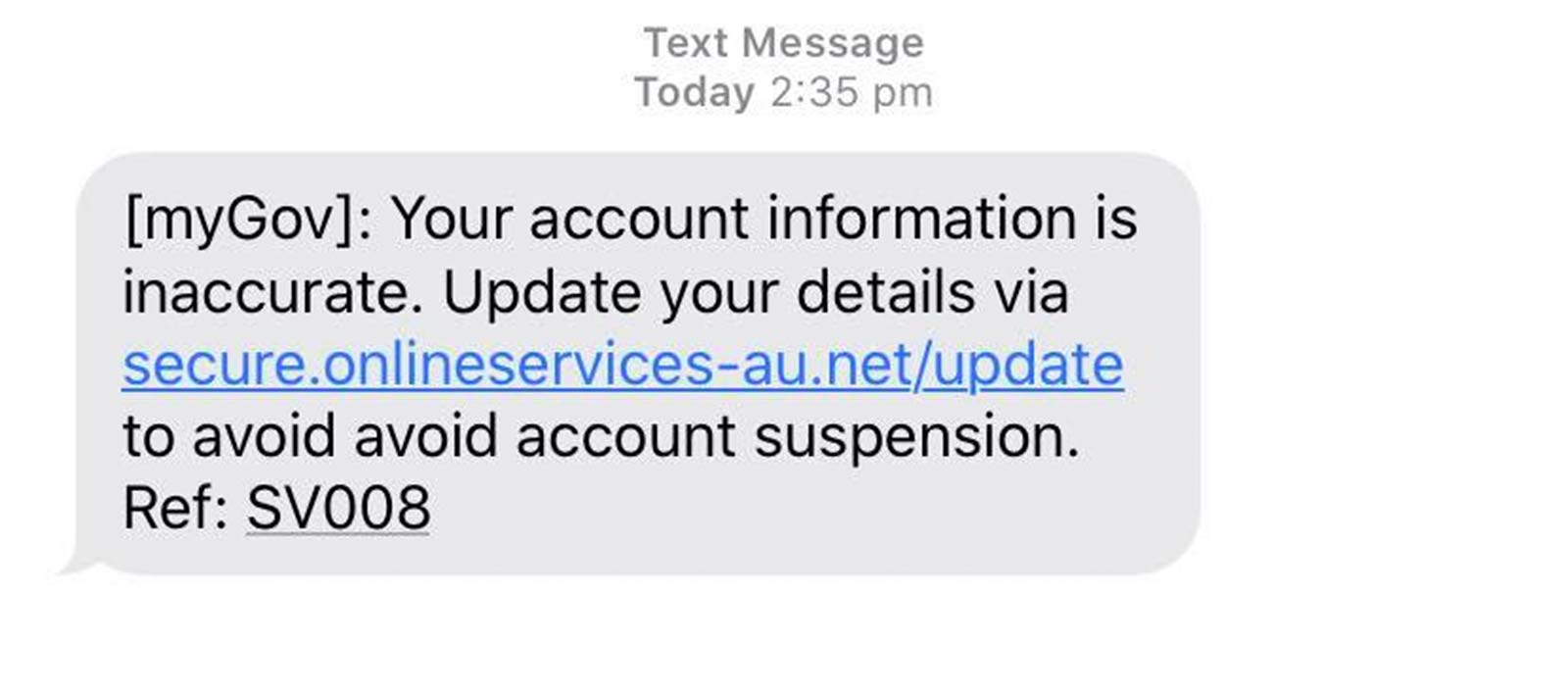
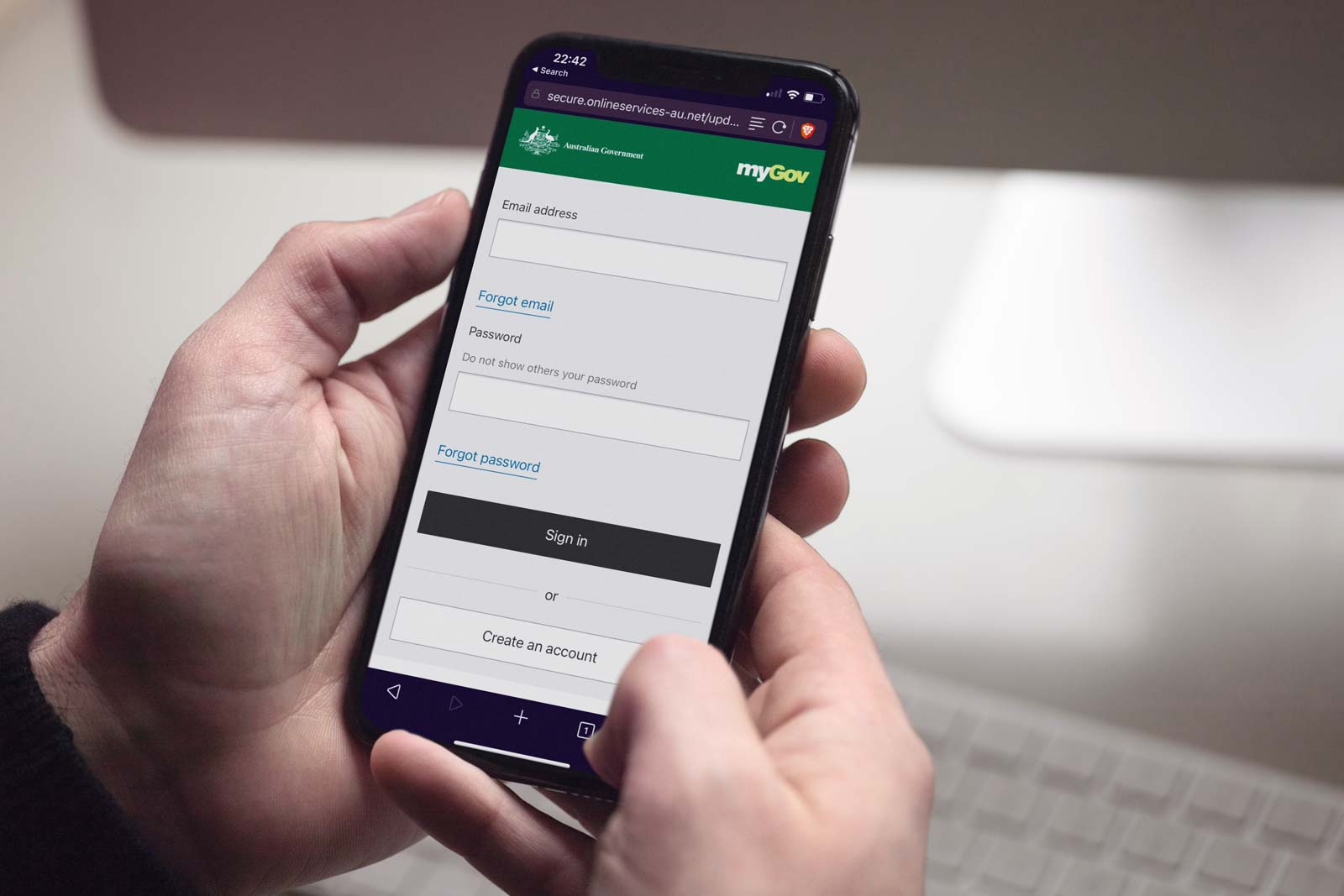
The message arrived from an Australian mobile number alluding to be from “myGov”, with information that “your account information is inaccurate”, complete with a link for you to change it.
However that link that will lead to a honeypot, with the scammers attempting to brazenly steal logins for Australia’s myGov. Even if they weren’t successful, there’s a good chance that similar passwords might be used between accounts, potentially giving a criminal access to your accounts in other places.
So how can we tell these messages are fakes, and how do you tell if a fake myGov SMS arrives in your phone’s inbox?
Read the SMS carefully
Scammers prey on individuals who don’t thoroughly check their messages, reading them quickly with hardly more than a passing glance. That quick glance means you’ll take in some of the information, but not the entirety, and anything you miss could just save you a click.
In the case of the myGov SMS scam making the rounds, the details you need to look for are the same as they are in every other SMS scam, so while there’s nothing new here, the message is still the same: read the SMS carefully before clicking on anything.
Anyone can get fooled, though, so let’s pull this apart bit by bit.
Check the sender ID
The first thing you should check is the sender ID.
That’s typically a phone number at the top of the message, but if something is coming from a company or a government department, it will often be a name, because that can be set for the service by whichever SMS system they’re sending out with.
At most SMS services, some names are forbidden because of the problem with scammers, but criminals can get close, so this can be a bit of a red herring.

In this scam, the criminals didn’t even attempt to give themselves an official ID, and instead just left a mobile number in there.
That should be a dead giveaway: this isn’y myGov, because you’d see myGov in that spot instead if it were even close to legit.
But it’s not the only hint that this message is a phishing scam.
Read the link, but don’t click
“Phishing” is called that because a scammer is attempting to go fishing for your details, typically by pretending to be something else. While the messaging can deliver this, when a scammer attempts to con you, they’ll often use a link with a site designed to look like the real thing.
That might sound like a difficult endeavour, but it can be really easy to create imitation sites that are only designed to look like the real thing, but not function the way the real site does.
They’re a copycat, and often a bad one, built merely to capture your details and leave you trying to work out why your ID and password won’t work on the website. You’ll eventually realise, albeit a bit too late.
The key to beating these sites — also called a “honeypot” — is to read the link carefully before clicking, and you probably won’t want to do that.
You see scammers can’t use the same website name as the real place — the domain, the www dot whatever you normally see. They can’t use the government domain “.gov.au” that myGov uses because:
- They’re not the real site, and
- They’re not government.
Because they can’t fake that connection, they’ll often try to make a website link that is either rather close or rather outlandish. We’ve seen examples of both, but in this case, the domain used by the scammers was close enough to make someone think it was legit.
However, there are things we can do to determine the legitimacy of these links, and that’s without clicking: we find out who currently owns the website.
Find out who registered that domain
Website names — the www-dot-whatever — are leased by people from domain registrars. Paid for on a yearly basis, a website name costs ten or twenty bucks a year, and they can be used for nearly anything.
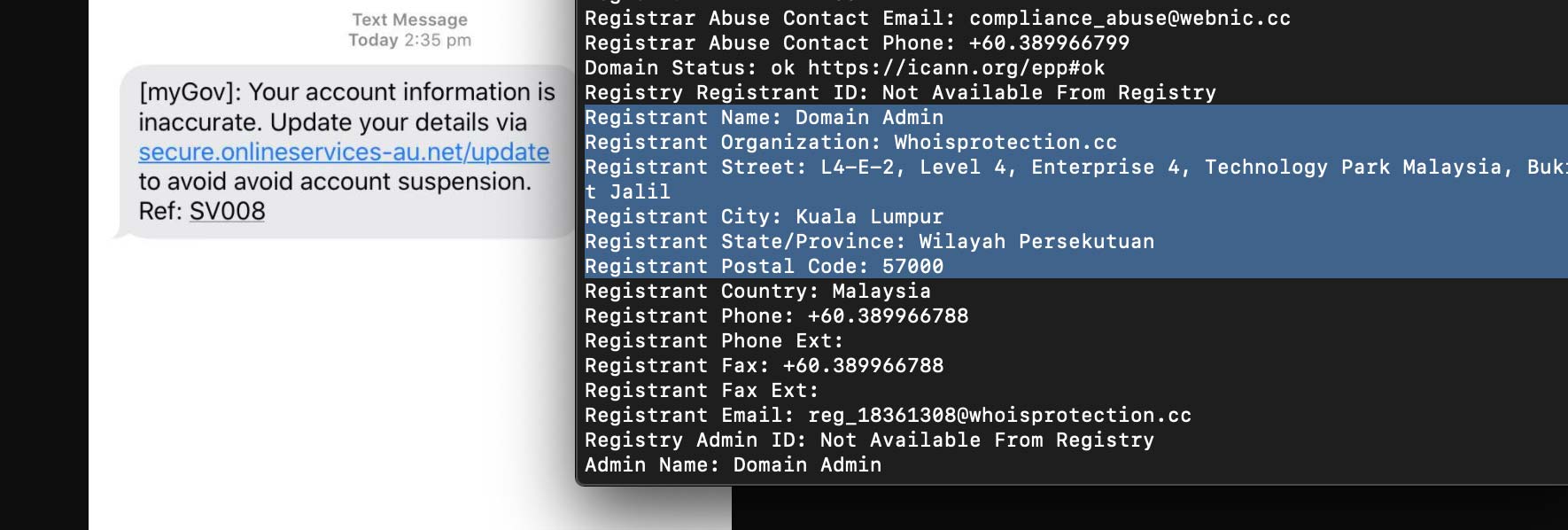
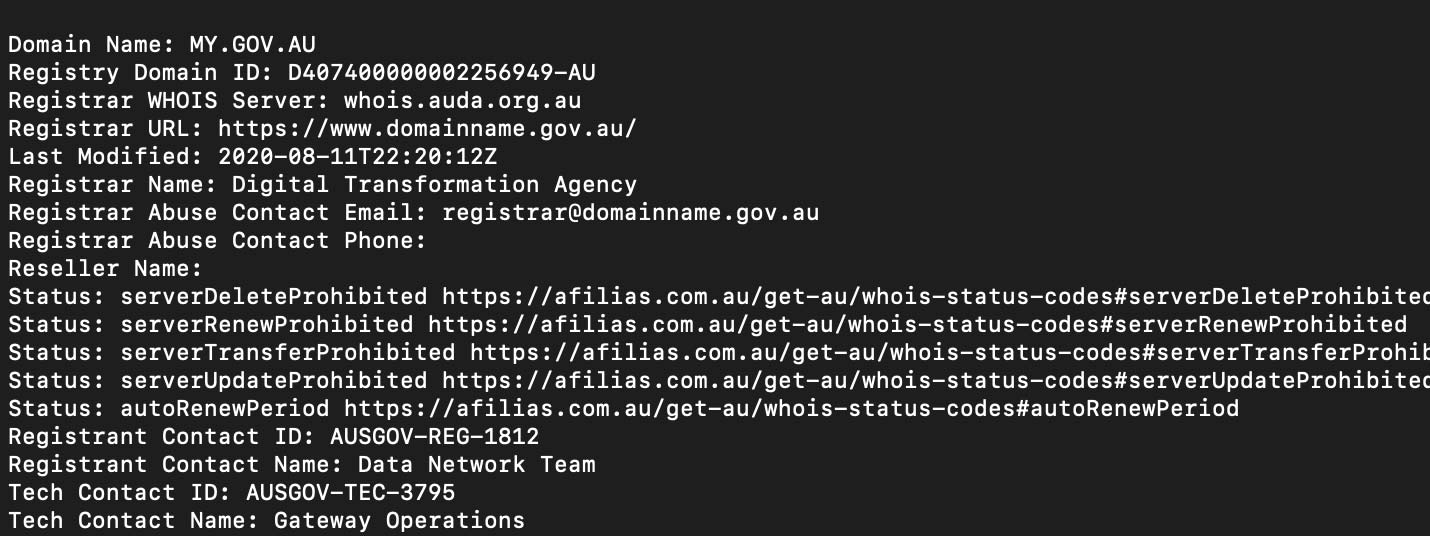
It’s a bit of a technical thing, but you can use online services or some of the tools built into some operating systems to find out who currently has control of that website. The process is called a “whois”, and it’s basically a way to find out who registered the website to begin with. Some of the people who did this might be hidden behind privacy settings, but you can typically find them out quickly and easily.
And when we searched for the ones behind the myGov scam doing the rounds, we found it was someone in Malaysia that had bought this website name.
That’s a dramatic difference from the government connections that sit behind the standard myGov website.
The point is there’s a fairly quick way to work out whether the link you think is real is indeed that way, even if it feels a little technical for most.
If something feels fishy, search for the real link
Ultimately, if you get a message that feels fishy, don’t click the link. Don’t ever click the link.
Instead, if you’re concerned, try Googling for the real link, or type it in as you already know it. Don’t use the link that’s been sent to you, because that’s just taking you back down this path once more.
If you’re sent a message that looks like myGov, search for “myGov” on Google and click on the link that pops up. Google won’t likely give you the fake one, and instead will deliver the real one, so there’s less a chance you’re going to fall for a scammer’s honeypot and instead get taken to the real site.
But scammers typically hope you’ll forget about this, and just click on the link, and that’s one thing you definitely shouldn’t do.